
Nine Iranian citizens—working at the behest of the government of Iran—have been charged in a massive computer hacking campaign that compromised U.S. and foreign universities, private companies, and U.S. government entities, including the Department of Labor and the Federal Energy Regulatory Commission.
The hackers were affiliated with the Mabna Institute, an Iran-based company created in 2013 for the express purpose of illegally gaining access to non-Iranian scientific resources through computer intrusions. Members of the institute were contracted by the Islamic Revolutionary Guard Corps—one of several entities within the Iranian government responsible for gathering intelligence—as well as other Iranian government clients.
During a more than four-year campaign, these state-sponsored hackers “compromised approximately 144 U.S.-based universities and 176 foreign universities in 21 countries,” said FBI Deputy Director David Bowdich during a press conference today at the Department of Justice in Washington to announce the indictments. When the FBI learned of the attacks, he said, “we notified the victims so they could take action to minimize the impact. And then we took action to find and stop these hackers.”
Initially, the cyber criminals used an elaborate spearphishing campaign to target the e-mail accounts and computer systems of their victims, which in addition to the universities included nearly 50 domestic and foreign private-sector companies, the states of Hawaii and Indiana, and the United Nations.
According to the indictments unsealed today in a Manhattan federal court, the hackers stole more than 30 terabytes of academic data and intellectual property—roughly three times the amount of data contained in the print collection of the Library of Congress.
“Their primary goal was to obtain user names and passwords for the accounts of professors so they could gain unauthorized access and steal whatever kind of proprietary academic information they could get their hands on,” said a special agent who investigated the case from the FBI’s New York Division. “That information included access to library databases, white papers, journals, research, and electronic books. All that information and intellectual property was provided to the Iranian government,” he added.
Mabna Institute targeted more than 100,000 accounts of professors around the world and successfully compromised approximately 8,000 of those accounts. The campaign continued through at least December 2017. Although it is difficult to calculate a dollar loss amount, through the course of the conspiracy, U.S.-based universities spent approximately $3.4 billion to procure and access data that the Iranians accessed for free because of their criminal activity.
“The hackers did their homework,” the cyber agent said. They conducted online reconnaissance of professors to determine the individuals’ research interests and the academic articles they had published. Armed with that information, they sent spearphishing e-mails to their targets—messages that appeared to be from professors at other universities.
Victim professors believed they were dealing with colleagues who had expressed an interest in academic articles. The e-mails tricked many of the professors to click on links that recorded their keystrokes when they signed into what they thought were their secure university domains but were actually bogus sites controlled by the hackers.
The Iranians targeted data across all fields of research and academic disciplines, including science and technology, engineering, social sciences, medical, and other professional fields.
In addition to targeting universities, the hackers gained access to employee e-mail accounts at nearly 50 private companies around the world—the majority of them U.S. firms. Among the U.S.-based victims were academic publishers, media and entertainment companies, technology companies, and investment firms. During that same period in 2016, the hackers also began conducting intrusions against various U.S. federal agencies and other organizations such as the United Nations.
This brute force technique involves collecting lists of names and e-mail accounts through open-source Internet searches and then guessing the users’ passwords, betting that some users never changed default company passwords or used common ones such as “password123.” Password spraying is such an unsophisticated technique that it can go undetected by company security networks. “They were flying under the radar,” said the cyber agent who investigated the case, “and the magnitude of their effort was remarkable.”
The tactic worked, providing hackers access to victims’ entire e-mail accounts. Now, in addition to academic data, the hackers were accessing companies’ trade secrets and sensitive U.S. government information.
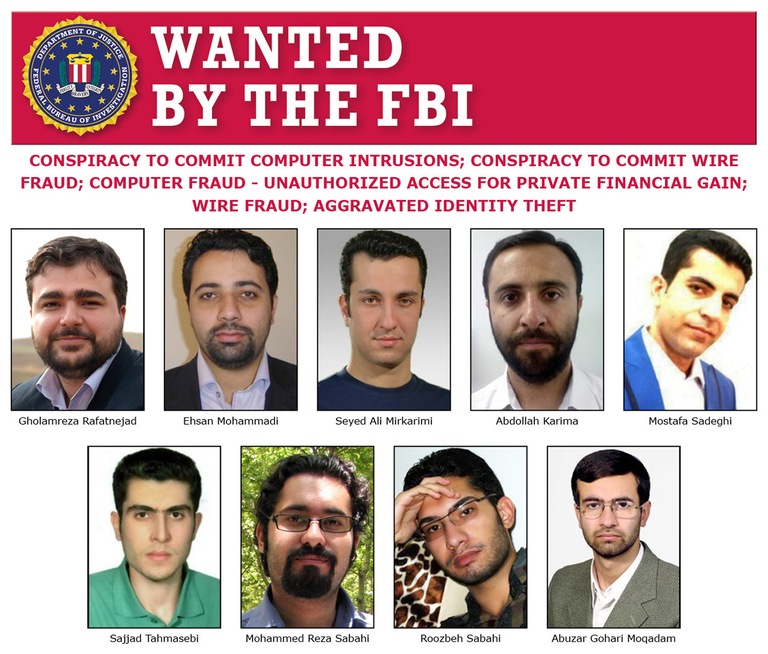
The nine defendants, who all reside in Iran, have been charged with conspiracy to commit computer intrusions, wire fraud, unauthorized access of a computer, and aggravated identity theft.
Bowdich acknowledged that apprehending the Iranian cyber criminals presents a challenge, “but it’s not impossible.” He explained that the defendants might travel outside of Iran and be subject to arrest. “Where we can’t apprehend these individuals quickly,” he added, “we will resort to different methods—naming and shaming, sanctions, and a lot of publicity. We will keep at it,” he said, “because the FBI and our partners at the Department of Justice have a very long memory.”


