The line between cyber offense and defense is disappearing—but the law still treats them very…
As one of his first acts in office, President Trump rescinded President Biden’s executive order imposing basic…
Russia is winning UN cyber governance—procedurally. Democracies must start leading on a new, positive agenda…
Before the executive branch deploys advanced AI systems in its most abuse-prone functions, it should…
You open a free app to do one simple thing. Before you even start, a…
Post-2022 efforts use ad buys to reach millions—drawing real reactions, Community Notes, and appeals to…
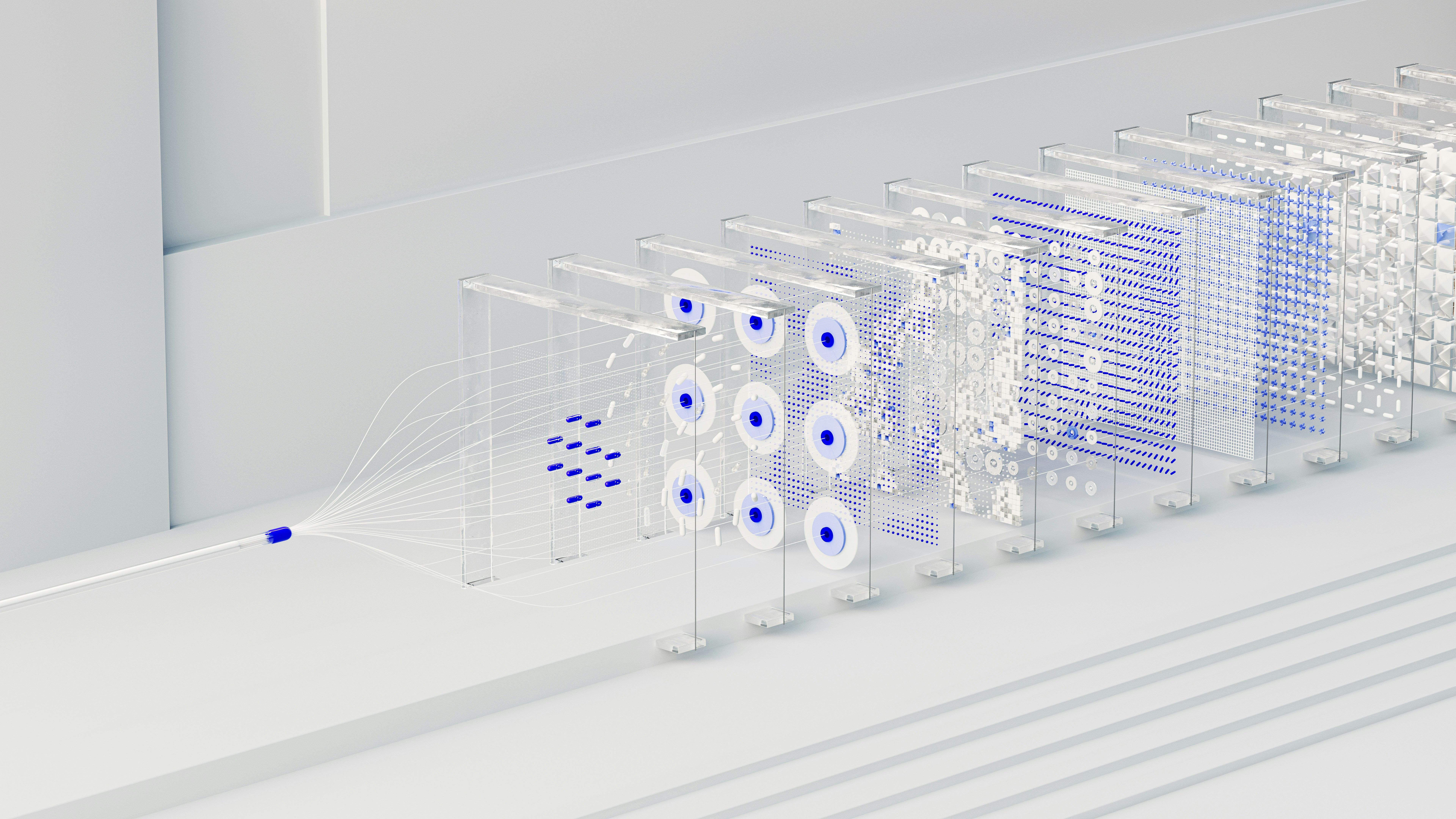
AI dominance will require more than faster models—it will require breakthroughs in understanding, testing, and…
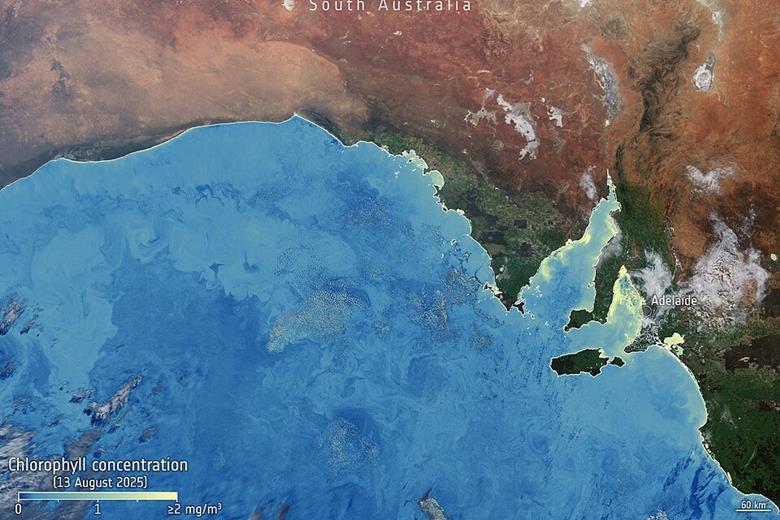
Identifying and analysing climate risks is a necessary function of governments, but researchers at Adelaide…
In the 1300s, the Black Death swept across Europe, killing 30 to 50 percent of…
The rapid proliferation of small, unmanned aircraft systems (UAS) has transformed what was once a…




.jpg?sfvrsn=d7b2f221_7)


.jpg?sfvrsn=bcbf98c2_5)