A Russian government-backed hacking team successfully hacked into Microsoft’s corporate network and stole emails and…
The U.S. position in the global value chain puts it at a disadvantage, and Washington’s…
National security agencies should turn their commitment to accountability in handling personal data into an…
This newsletter is part of a collaboration between Lawfare and Risky Business. You can find the full…
Illinois Institute of Technology (Illinois Tech) has received a substantial grant from the National Science Foundation (NSF) to…
A FAMU-FSU College of Engineering researcher is developing technology to protect the electric grids of…
The keys to effective AI regulation are hiding in plain sight. The November 2023 implosion of OpenAI—the…
AI self-regulation may not be enough. It’s time to consider licensing regimes that apply throughout…
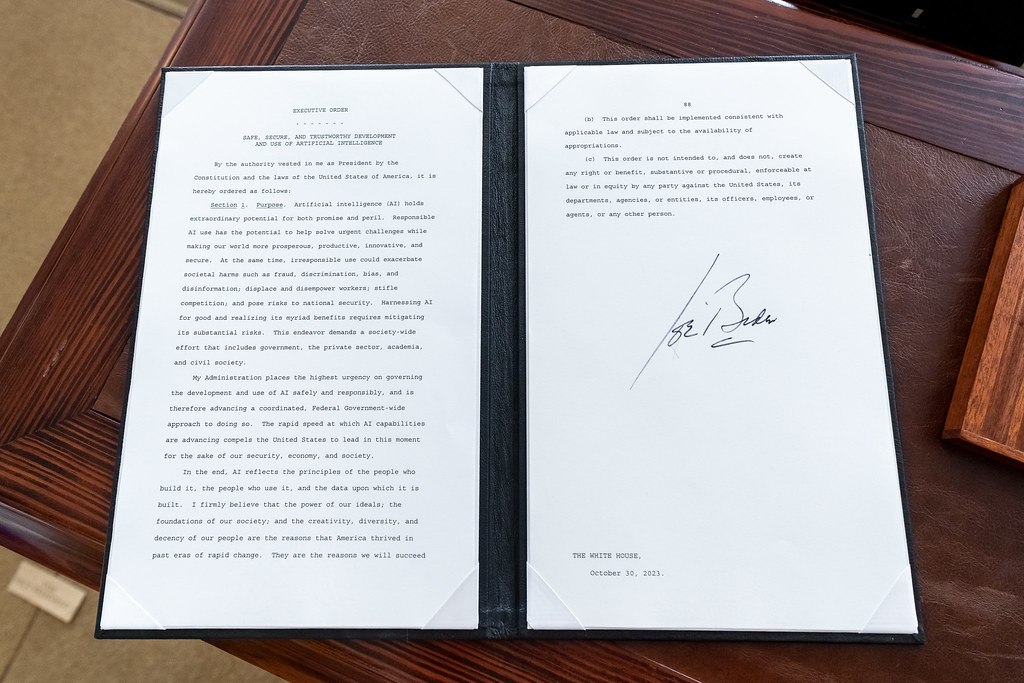
A summary of the Executive Order on the Safe, Secure, and Trustworthy Development and Use…
Cybersecurity experts are warning of “significant” data privacy risks after a Vancouver rape crisis centre…