In January 2020, Debi Gamber studied a computer screen filled with information on scores of check deposits. As a manager for eight years at a TD Bank branch in the Baltimore suburb of Essex, she had reviewed a flurry of account activity as a security measure. These transactions, though, from the ATM of a tiny TD location nestled in a nearby mall, struck her as suspicious.
Time and again, Gamber saw that these checks were payable to churches – many states away from the Silver Spring shopping center branch – yet had been deposited into personal accounts, a potential sign of theft.
Digging deeper, she determined that the same customer service representative, Diape Seck, had opened at least seven of the accounts, which had received more than 200 church check deposits. Even fishier, the purported account holders had used Romanian passports and driver’s licenses to prove their identities. Commercial bankers rarely see those forms of ID. So why were all these Romanians streaming into a small branch located above a Marshall’s clothing store?
Suspecting crimes, Gamber submitted an electronic fraud intake form, then contacted TD’s security department to inform them directly of what she had unearthed. Soon, the bank discovered that Seck had relied on Romanian documents for not just seven accounts but for 412 of them. The bank phoned local police and federal law enforcement to report that an insider appeared to be helping criminals cheat churches and TD.
Nine months after TD’s tip, agents started rounding up conspirators, eventually arresting nine of them for crimes that netted more than US$1.7 million in stolen checks. They all pleaded guilty to financial crimes except for Seck, who was convicted in February 2023 for bank fraud, accepting a bribe and other crimes. He was sentenced in June 2023 to three years in prison.
Sophisticated crimes
How could it happen? How could criminals engineer a yearlong, multimillion-dollar fraud just by relying on a couple of employees at two small bank branches in a scheme with victims piling up into hundreds?
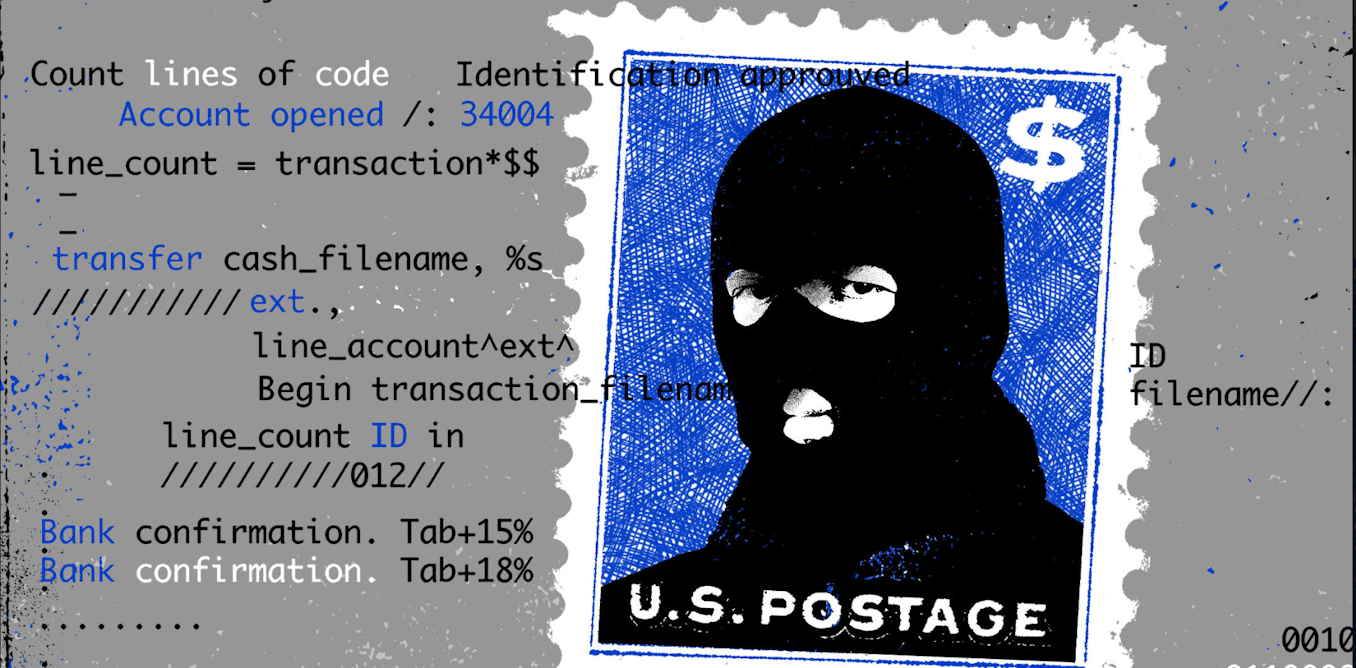
The answer is, because it’s easy. Crimes like these happen every day across the country. Scams facilitated by deceiving financial institutions – from international conglomerates to regional chains, community banks, and credit unions – are robbing millions of people and institutions out of billions and billions of dollars. At the heart of this unprecedented crime wave are so-called drop accounts created by street gangs, hackers and even rings of friends. These fraudsters are leveraging technology to obtain fake or stolen information to create the drop accounts, which are then used as the place to first “drop” and then launder purloined funds.

To better understand the growing phenomenon of drop accounts and their role in far-reaching crime, the Evidence-Based Cybersecurity Research Group at Georgia State University joined The Conversation in a four-month investigation of this financial underworld. The inquiry involved extensive surveillance of criminals’ interactions on the dark web and secretive messaging apps that have become hives of illegal activity. The reporting shows:
- The technological skills of street gangs and other criminal groups are exceptionally sophisticated, allowing them to loot billions from individuals, businesses, municipalities, states and the federal government.
- Robberies of postal workers have escalated sharply as fraudsters steal public mailbox keys in the first step of a chain of crimes that ends with drop accounts’ being loaded with millions in stolen funds.
- A robust, anonymous online marketplace provides everything an aspiring criminal needs to commit drop account fraud, including video tutorials and handbooks that describe tactics for each bank. The dark web and encrypted chat services have become one-stop shops for cybercriminals to buy, sell and share stolen data and hacking tools.
- The federal government and banks know the scope and impact of the crime but have so far failed to take meaningful action.
“What we are seeing is that the fraudsters are collaborating, and they are using the latest tech,” said Michael Diamond, general manager of digital banking at Mitek Systems, a San Diego-based developer of digital identity verification and counterfeit check detection systems. “Those two things combined are what are driving the fraud numbers way, way up.”
Billions stolen
The growth is staggering. Financial institutions reported more than 680,000 suspected check frauds in 2022, nearly double the 350,000 such reports the prior year, according to the Treasury Department’s Financial Crimes Enforcement Network, also known as FinCEN. Through internet transactions alone, swindles typically facilitated by drop accounts cost individuals and businesses almost $4.8 billion last year, a jump of about 60% from comparable fraud losses of more than $3 billion in 2020, the Federal Bureau of Investigation reported.
Plus, a portion of the estimated $64 billion stolen from just one COVID-19 relief fund went to gangsters who rely on drop accounts, according to a congressional report and an analysis from the University of Texas at Austin. Criminals using drop accounts also hit the pandemic unemployment relief funds, which experienced improper payments of as much as $163 billion, the Labor Department found. Indeed, experts say the large sums of government money meant to combat economic troubles from COVID-19 fueled the rapid growth of drop account fraud, as trillions of dollars in rescue funds were disbursed in the form of wires and paper checks.
“There were a huge range of criminals who were trained in this during the pandemic,” said one banking industry official who spoke on condition of anonymity because of the sensitivity of the matter. “A lot of them have grown up in the pandemic and seen that it is easy to make a lot of money with these schemes, with very little risk of prosecution.”
David Maimon, Professor of Criminal Justice and Criminology, Georgia State University and Kurt Eichenwald, Senior Investigative Editor, The Conversation
This article is republished from The Conversation under a Creative Commons license. Read the original article.



