A major IT outage has hit businesses across the world, grounding planes as well as…
THREATS
The US military recently launched a groundbreaking initiative to strengthen ties with the commercial space…
Our latest research has found that clickable links on websites can often be redirected to…
Internet users leave many traces on websites and online services. Measures such as firewalls, VPN…
Cyber operations reveal their limitations as means of warfare, but territorial conquest opens unique opportunities…
Affected Platforms: Microsoft Windows Impacted Users: Microsoft Windows Impact: Compromised machines are under the control of the threat…
China Turns to Private Hackers as It Cracks Down on Online Activists on Tiananmen Square Anniversary
Every year ahead of the June 4 commemoration of the Tiananmen Square massacre, the Chinese…
Spamouflage is famous for being widespread and ineffective. A new tactic targeting Trump supporters suggests…
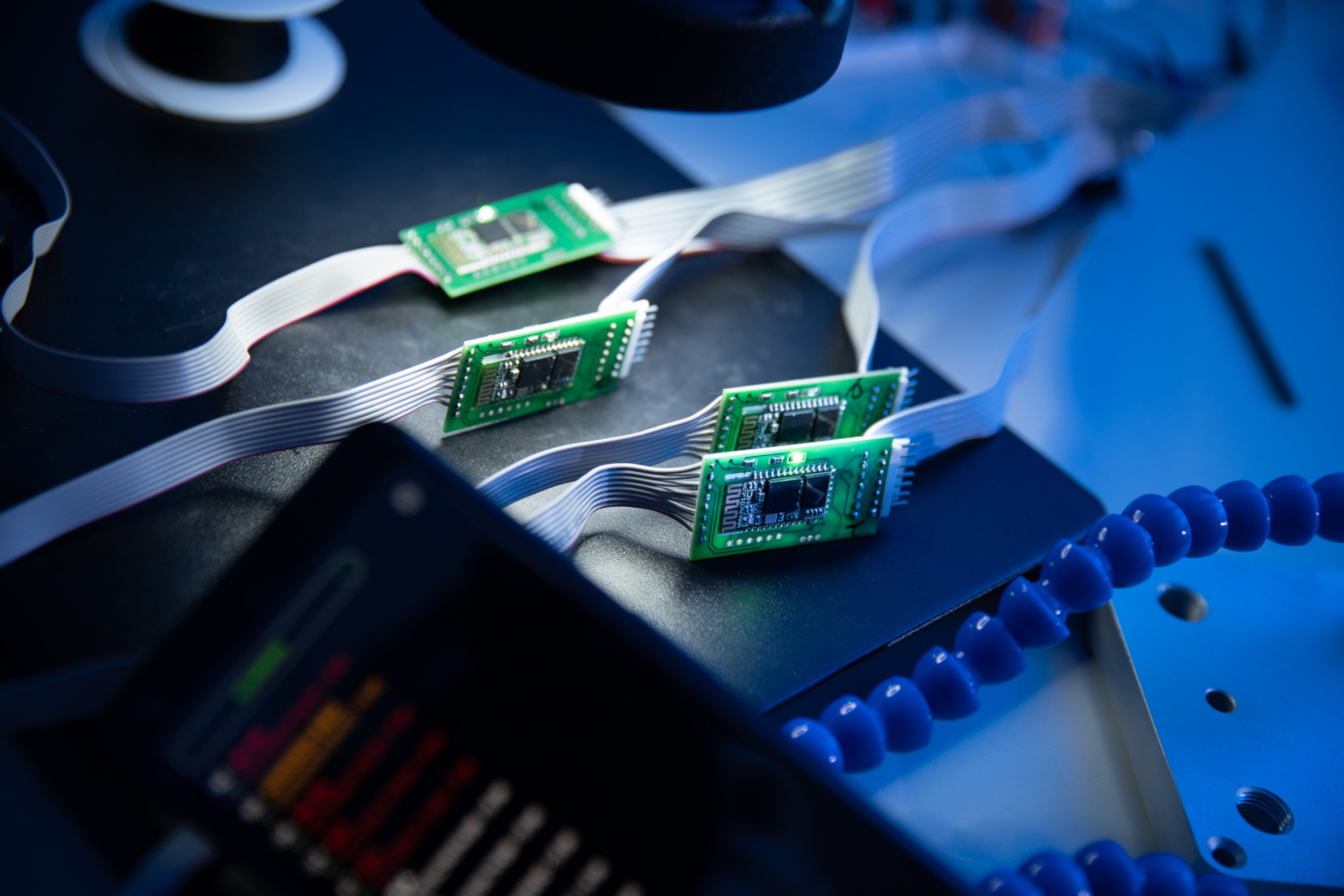
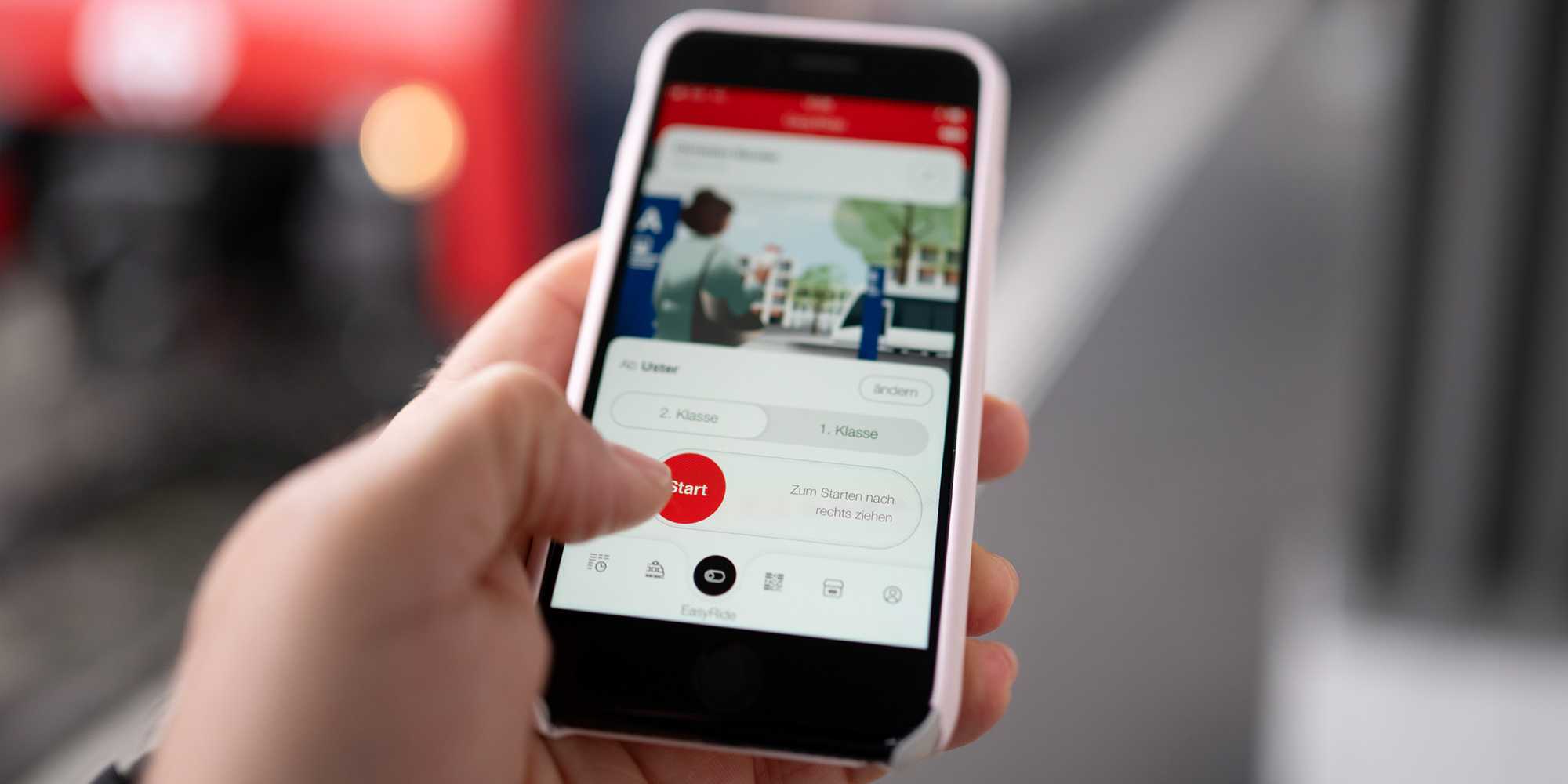
Experiments by ETH Zurich computer security researchers showed that smartphones can be manipulated to allow…
On a cold winter night in 2016, Ukrainians experienced the first-ever known blackout caused by…