A new report has found that Asian crime syndicates have integrated new service-based business models and technologies…
STRATEGY & THREATS
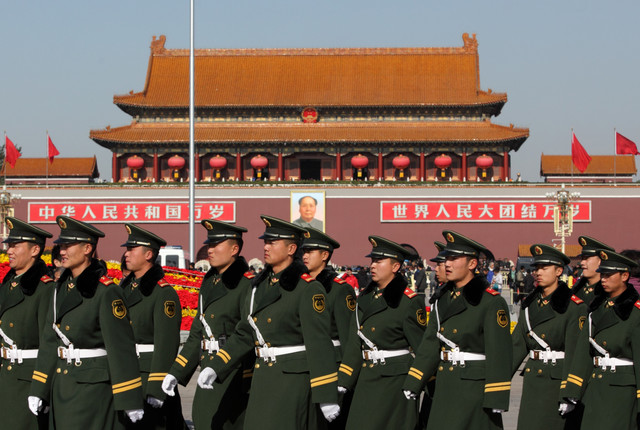
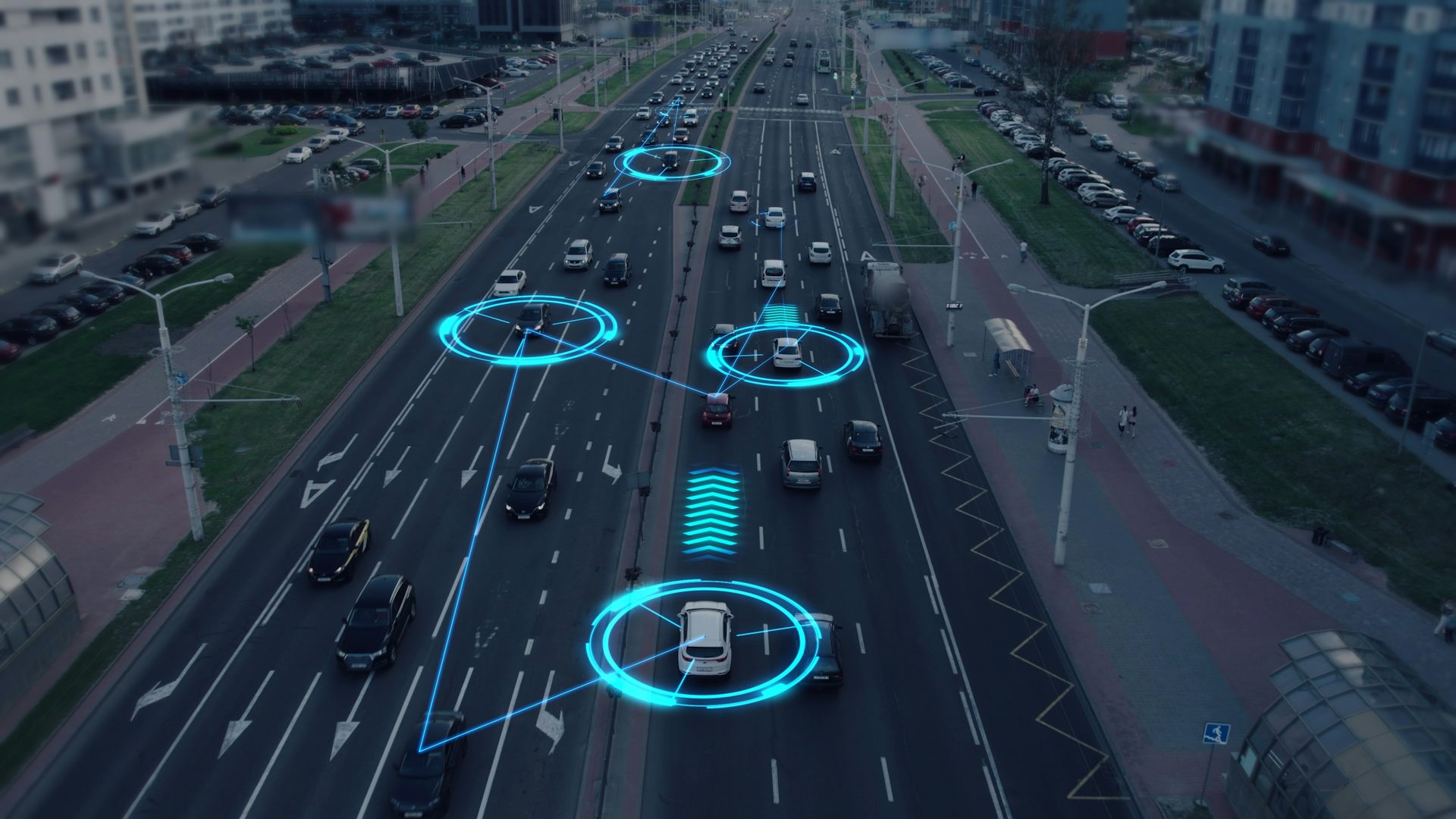
In April, US lawmakers urged President Joe Biden to ban Chinese-built electric vehicles (EVs), labelling…
The explosions—more an assault via supply chain than a cyberattack—raise fears that even low-tech devices…
How new statutory prohibitions and long-standing tort claims can combat pernicious election lies when voter…
AI-generated content likely enjoys broad First Amendment protection, but remains subject to defamation laws and…
Insights Into Chinese Use of Generative AI and Social Bots from the Career of a…
Chinese defense experts worry that AI will make it more difficult for Beijing to control…
Central Oregon Pathology Consultants has been in business for nearly 60 years, offering molecular testing…
The sheer scale of the breach and the way in which the data was first…
Iran’s sustained digital interference in U.S. elections now includes hack-and-leak tactics. Here’s how its strategy…



.jpg?sfvrsn=1908419f_5)