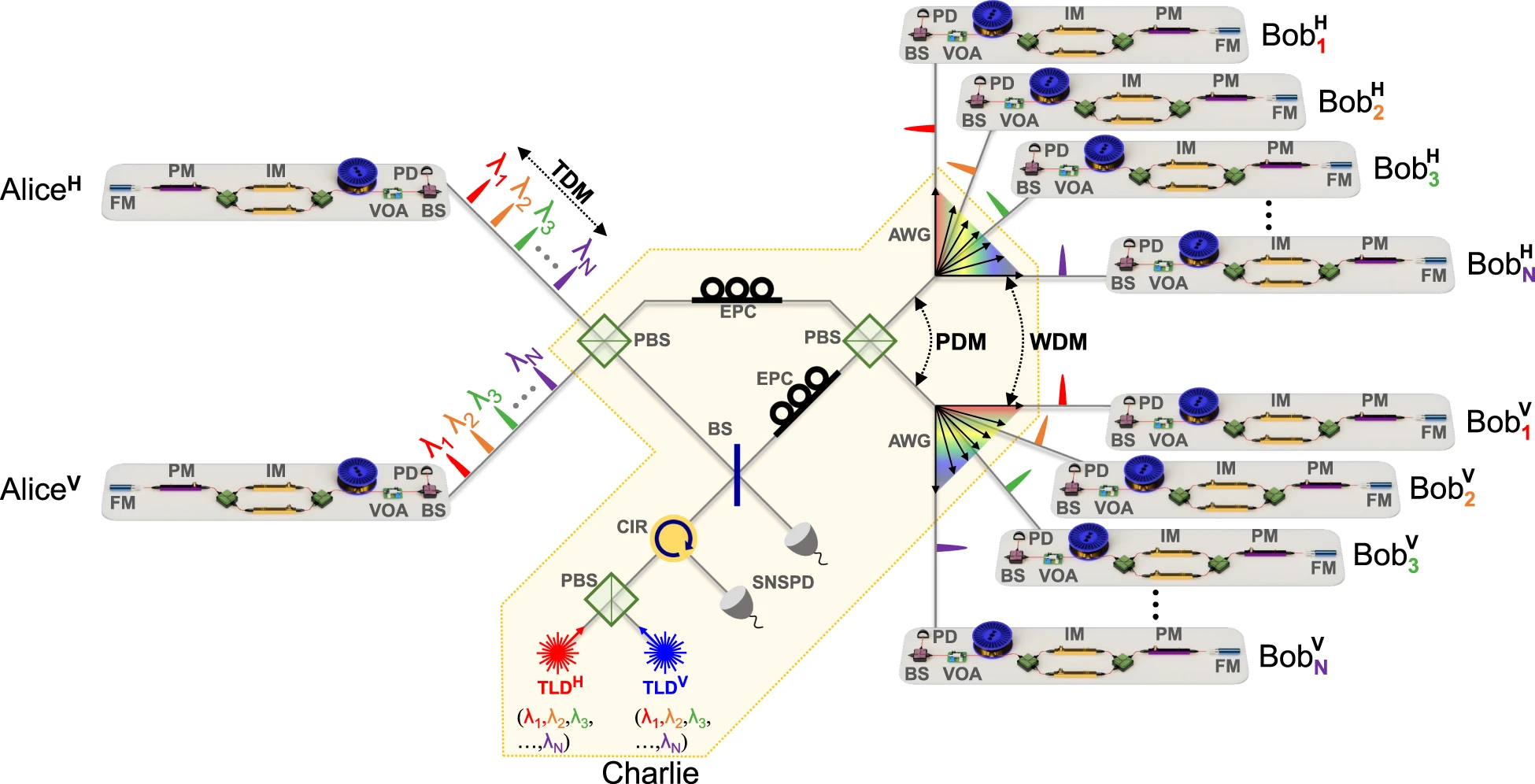
Researchers at Cornell University have developed a mechanism for preserving anonymity in encrypted messaging –…
STRATEGY & THREATS
Training a machine-learning model to effectively perform a task, such as image classification, involves showing…
In modern cryptosystems, users generate public and private keys that guarantee security based on computational…
The Cybersecurity and Infrastructure Security Agency (CISA) has released a new advisory suggesting North Korean…
Aon recently disclosed that 145,889 of its North American customers had their sensitive information exposed…
Researchers reviewed 42 apps and found privacy and security deficiencies, some of which were quite…
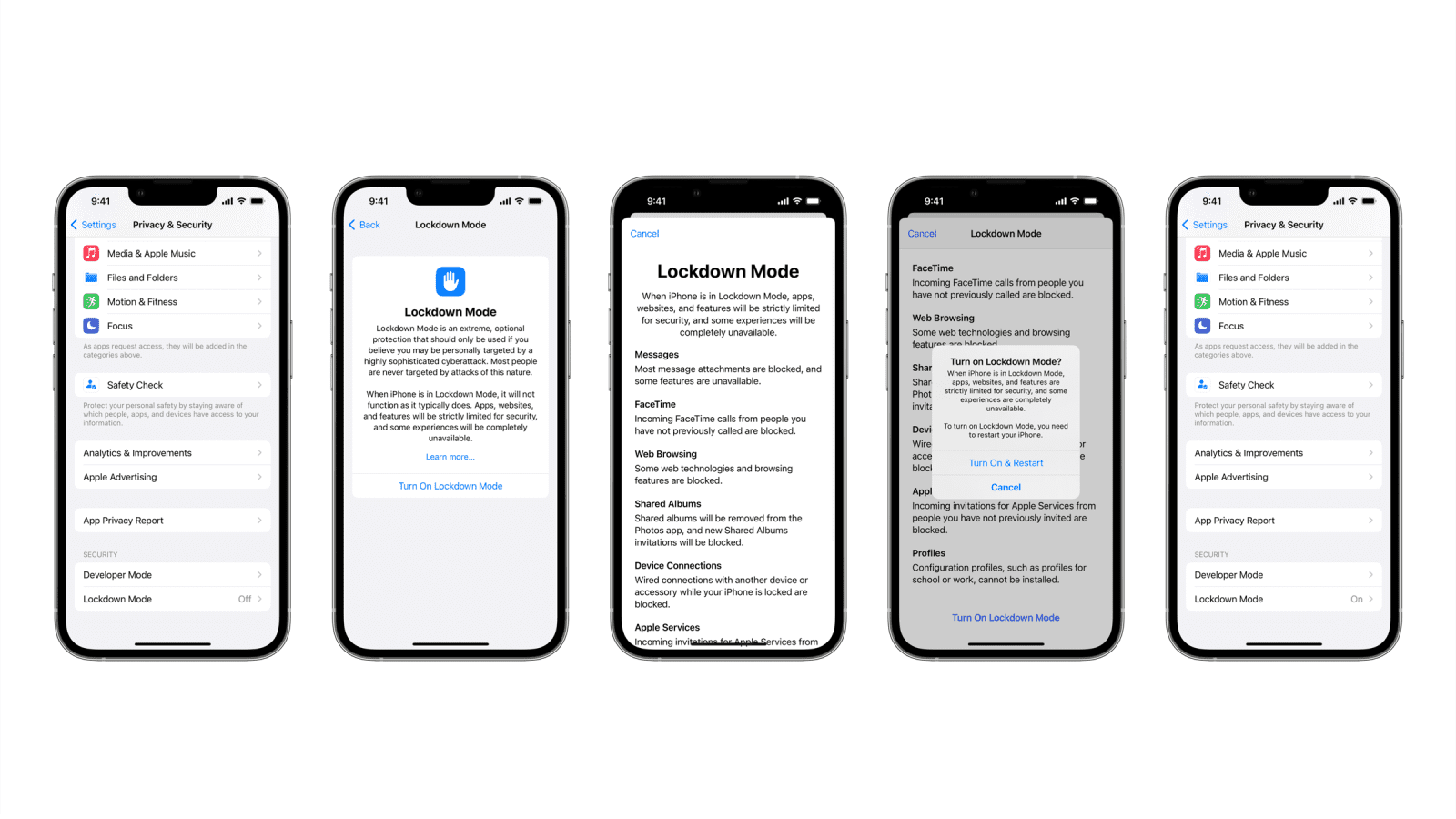
Apple has announced a new set of iPhone features called “Lockdown Mode.” Unveiled in a blog post on…
Solar panels and wind turbines, now projected to produce 44% of America’s electricity by 2050,…
Researchers are pushing to outpace hackers and develop stronger protections that keep data safe from…
Using artificial intelligence (AI) for warfare has been the promise of science fiction and politicians…