You open a free app to do one simple thing. Before you even start, a full-screen message asks whether you want to try the paid version. The “Start free trial” button is…


You open a free app to do one simple thing. Before you even start, a full-screen message asks whether you want to try the paid version. The “Start free trial” button is…

Post-2022 efforts use ad buys to reach millions—drawing real reactions, Community Notes, and appeals to Grok. In August 2022, Stanford Internet Observatory and Graphika published “Unheard Voice,” a report analyzing pro-Western influence…
.jpg?sfvrsn=bcbf98c2_5)
AI dominance will require more than faster models—it will require breakthroughs in understanding, testing, and securing frontier AI. A fundamental tension previously defined the artificial intelligence (AI) policy landscape: Proposals for the…
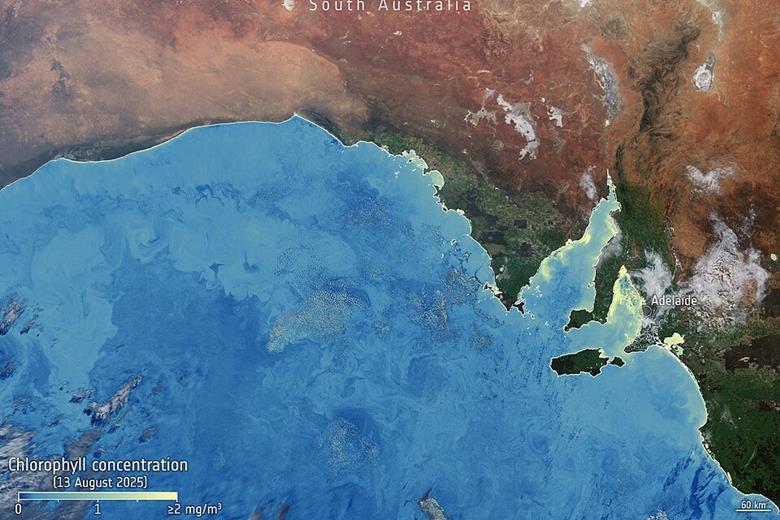
Identifying and analysing climate risks is a necessary function of governments, but researchers at Adelaide University’s Environment Institute argue such processes will not lead to effective action without taking additional steps to…

In the 1300s, the Black Death swept across Europe, killing 30 to 50 percent of the continent’s population. The loss of nearly one-third of the continent’s labor supply caused wages to rise…

The rapid proliferation of small, unmanned aircraft systems (UAS) has transformed what was once a limited aviation concern into a persistent challenge for force protection and homeland defense. Commercially available drones now…

The U.S. debate over how to respond to China’s artificial intelligence (AI) capabilities contains a structural blind spot that neither side has engaged. The most commonly proposed response, tighter export controls, does…
-security.jpg)
Mythos Fallout, U.S. Government Weighs AI Model Regulation The Trump administration is considering applying stricter oversight to American artificial intelligence (AI) models due to their cybersecurity impact. However, before pulling the trigger…

Worker protections and concerns about economic stability may slow the adoption of new technology. Editor’s Note: Artificial intelligence (AI) is shaking up China’s economy, just as it is raising many questions in…